Spear Phishing: The ADA hack
By Tasha Dickinson, Founder and Chief Technologist of Siligent.
The American Dental Association (ADA) suffered a ransomware attack this past weekend. (April 22, 2022)
Their official statement was:
“ADA recently experienced a cybersecurity incident that caused a temporary disruption to certain computer systems. Upon discovery, ADA immediately responded by taking affected systems offline.”
A new ransomware gang named Black Basta took credit when they leaked sensitive information onto the dark web. The threat actors claim that up to 30% of all data stolen has already been leaked by the group in an attempt to further negotiations for a ransom.
This brings two warnings to all of us in the dental world:
- Threat actors will not hesitate to release Personal Health Information (PHI) in order to gain funds, and in most cases, release the PHI even if they are paid. Prevention is the only way to safeguard PHI.
- The dental world continues to be very vulnerable to spear phishing attacks.
We at Siligent would like to give you a quick overview on how to prevent becoming a victim. We do not want your practice to be the one releasing thousands of PHI files and losing the credibility of your customers, not to mention thousands of dollars and hours of your time.
Training and knowledge are part of the solution, but so is cyber hygiene, backups, monitoring, and the right tools.
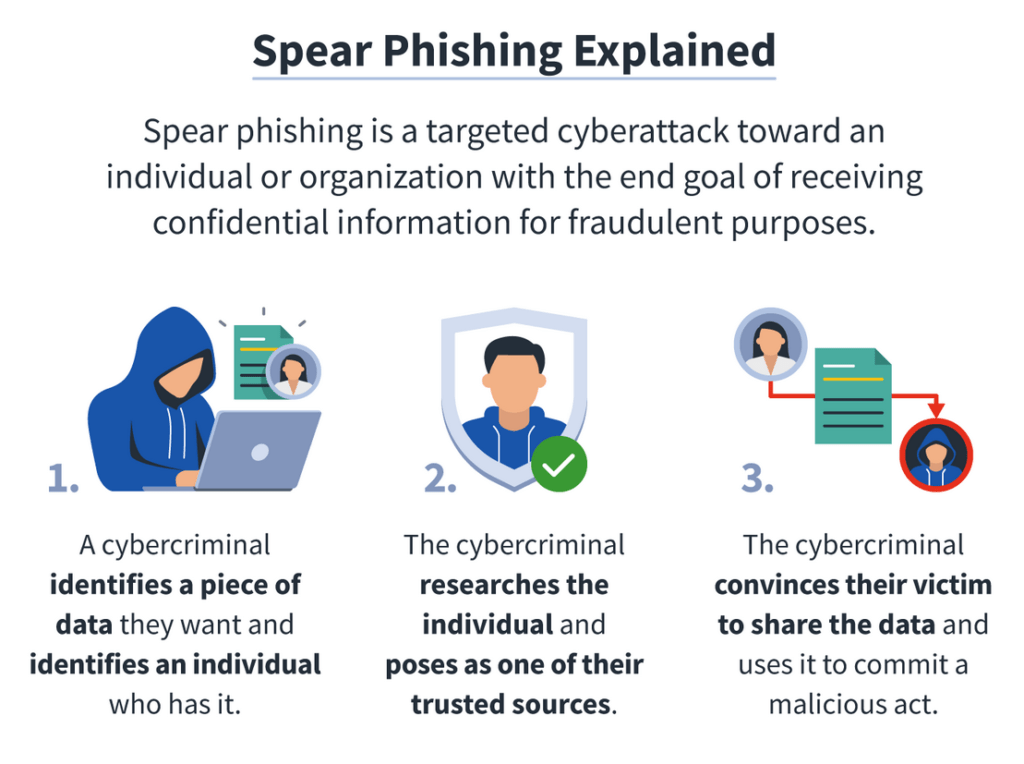
A spear phishing attack, as defined by the Oxford dictionary, is:
The fraudulent practice of sending emails ostensibly from a known or trusted sender in order to induce targeted individuals to reveal confidential information.
Thousands of hackers now have your email address, possibly a date of birth, or social security number. They also know that you are part of the ADA, are a dentist, have an interest in a specific class, or have shown interest in a product or service provided by the ADA.
They could craft an email like this example:
Dear Richard,
Thank you so much for downloading the HIPAA handbook on January 26th, 2022. Please find the updated information for 2022 here to adjust to recent changes in HIPAA standards passed by the Health and Human Services.
It might go on to talk about your practice, and have specific information about your order. When you click on the link to download the additional information, it might take you to a website to sign in to your account, or verify known information before signing in to the account. It would have the right header, have an email address from the ADA.com, or a similarly created fake email account (for those who are paying attention the ADA uses a .org domain listing).
The end result is that you give up a password or other piece of information they can use.
Threat actors are patient and they are smart. They are paid 6 figures just to gain passwords, usernames and access to systems. As of right now, threat actors have a higher chance of dying falling out of bed, than going to jail for stealing millions of dollars. Any dentists who are part of the ADA (is anyone not?!), are now at risk for a targeted spear phishing attack. Think you are too small for them to bother with? Check out my blog on the true cost of a ransomware attack.
So what can you do to prevent a spear phishing attack?
- Do not click on any link that you are not expecting.
- Hover over any link that you are even considering clicking on, and check the bottom left hand side of your screen to see if it’s taking you where it should.
- If at all possible, navigate directly to the website, and log in there.
- Pick up the phone to call and verify the email and the sender.
Not all spear phishing emails start with a link to click. Sometimes they are an elaborate series of emails that send you to a website, are verified through phone calls, linked in pages, and what appear to be valid websites.
How can we fight back? New software has emerged that can prevent or stop attacks. Threats constantly evolve, and so do our tools, but the basic premise is to trust nothing until it has been verified and validated.
At Siligent, we can help. Want to know if you’ve been compromised or if your information is out on the dark web? Contact us to conduct a quick scan and work with us to find a solution to help protect you and your business.
Register for this FREE
Dental FraudBuster On-Demand Course
You probably have heard the statistics, and they are not good.
3 out of every 5 dentists end up being embezzled. We can do better!
Complete the course to receive a “Proof of Course Completion” for 1 CEU.